Edge Computing: Bringing the Cloud to the User
As 5G networks are being widely deployed, followed by the first wave of 5G Standalone rollout, unprecedented volumes of data will continue to grow based on the rise in the number of connected devices. The massive scale and complexity of data created by connected devices impose a considerable challenge, pushing network bandwidth requirements to their limit.
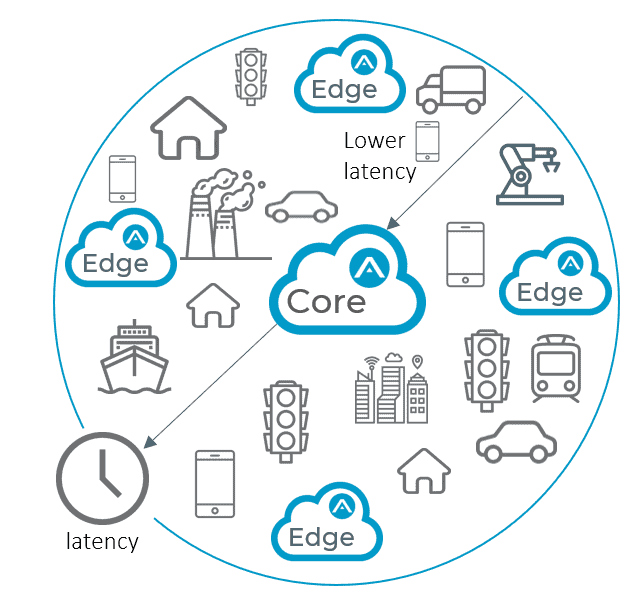
While the cloud offers unrivaled computing power and storage, sending all that device-generated data to a centralized data center or the cloud negatively impacts bandwidth and causes latency issues. Multi-Access Edge Computing (MEC) brings cloud resources to the network edge close to applications, connected devices, and end-users, eliminating the journey to the cloud data center.
Thus, with edge computing, the data is processed and analyzed closer to its point of origin. Operating from within the Radio Access Network (RAN), edge computing aims to enhance the user experience by reducing latency and ensuring highly efficient network operation and service delivery.
A new study by Juniper Research has found that network operator spend on MEC (Multi-access Edge Computing) will grow from $2.7 billion in 2020, to $8.3 billion in 2025[i]. Edge computing offers a new 5G ecosystem and value chain and the opportunity to develop new business models as an operator. By deploying edge computing, you can rapidly roll out new services for multiple use cases and vertical market use cases, helping differentiate your service offering portfolio. In addition, you can tap into new revenue streams by delivering innovative services closer to the end-user and improving the overall quality of experience.
Continue reading to learn how operators can smartly monitor this new distributed environment while gaining E2E visibility.
What is Edge Computing?
5G network relies on a distributed cloud foundation, housing data and applications in shared data centers for further processing. However, these data centers may often be located far from the end-user, creating an inherent distance between the user and the app, which can negatively impact bandwidth and throughput transfer rates.
Edge computing, often referred to as Multi-Access Edge Computing (MEC), physically moves data and apps away from data centers and closer to the end-user. Instead of transferring raw data to a central data center for processing and analysis, this process is performed where the data is generated. By decentralizing these data centers, edge computing offers localized cloud computing capabilities, putting the storage and servers where the actual information is located.
Operators can deploy edge computing at enterprise customers’ premises, retaining sensitive data in homes, trains, vehicles, or inside factory buildings. This enables the data to travel at high-rate speeds without traveling a long distance to a data center or a cloud.
Edge computing can be defined by:
- Proximity: edge computing is located close to the origin of information, enabling capturing critical data in real-time for advanced analytics capabilities. The direct connection between the edge and IoT devices can be used for developing business-specific applications.
- Lower latency: By running close to the end devices, the edge considerably reduces latency. This leads to faster response time, minimizing congestion of the network, and improving the latency-sensitive quality of experience for the end-user.
- On-premises: Since the edge is local, it is essentially isolated from the other parts of the network while retaining access to local resources.
These characteristics and capabilities offered by edge computing can be leveraged to allow proximity, speed, and agility to be used for broader innovation that can be translated into unique value and revenue generation for operators.
The Business Opportunity: Gain an Edge Ahead of Competition
According to the Million Insights report, the global edge computing market size is projected to reach USD 43.4 billion by 2027[ii]. As edge computing delivers proximity, low latency, high bandwidth, and real-time insights, it can be translated into a clear business value critical to successfully launching a 5G network.
As an operator with edge computing, you can transform your network into a digital infrastructure platform for dynamic service innovation. As a result, you can offer new business models to enterprise and vertical industries enabling them to deliver their business-specific or mission-critical apps without congestion. Powered by 5G, edge computing opens many new use cases such as V2X services, long-range remote control of drones, VR for gaming, and long-range remote control of factory robots.
Hence, you can capitalize your network, opening it to third-party players and flexibly exposing needed capabilities to applications and services. Moreover, with the development of new applications at the edge, making them aware of the local context in which they operate (locality, RAN conditions, etc.) can open up entirely new service categories and enrich the offering to your end-users.
The Monitoring Challenge
The network logic is distributed in different network nodes by moving to the edge, introducing new challenges and issues. Operators seeking to harness the power of edge computing and deliver on advanced capabilities to users must gain visibility into what happens at the edge.
As many data transactions are staying at the edge instead of going to data centers, you encounter new challenges in capturing the data for analysis and assessing network requirements as a whole. You will need to adopt distributed network monitoring capabilities between the edge, the data center, and the cloud. To overcome this challenge, you will need to instantiate an adaptive service assurance solution that hosts edge-assurance capabilities.
Assurance at the Edge
To exploit the full power of edge computing, operators’ service offering at the edge needs to meet stringent SLAs of business-specific use cases and applications. To do so, you must be able to detect network degradations and prevent service outages proactively. Thus, monitoring each edge-delivered service smartly, meeting agreed-upon SLAs – making assurance a critical success factor.
To achieve that, operators should deploy a cloud-based, distributed assurance solution to gain visibility into services at the edge to optimize the network performance and deliver the expected quality. A distributed assurance solution that is microservices-based can deploy micro-probes with a low footprint that are scalable at the edge. The micro-probes will be instantiated together with the network function itself to provide probing and troubleshooting capabilities, and also with a container-based orchestration system such as Kubernetes. Thus, the assurance solution can be deployed, scaled, and managed automatically.
Facilitated by micro-probes, assurance at the edge will deliver real-time intelligence so operators can proactively ensure these new low-latency service offerings. This will require built-in artificial intelligence and machine learning, so that network anomalies can be detected automatically and rectified before they affect the customer. Moreover, delivering a closed-loop approach to service assurance and policy management will become critical as these advanced edge services are rolled-out, and the amount of traffic continues to grow.
Summary
In conclusion, edge computing can transform the way data is being transmitted, processed, and delivered by millions of data sources globally. The proximity to data at its source can provide strong business benefits, including lower latency, near real-time insights, better bandwidth availability, and improved service quality. These benefits should be leveraged by operators who wish to differentiate themselves, getting ahead of the competition to creating new value chains.
To smartly monitor the edge, operators need to deploy an adaptive assurance solution that is essential to driving the demand for the edge’s innovative services and use cases.
To learn how to assure the lifecycle of your 5G network, download our latest infographic.
[i] https://www.juniperresearch.com/press/edge-computing-investment-by-network-operators
[ii] https://www.prnewswire.com/news-releases/edge-computing-market-size-to-expand-at-37-4-cagr-by-2027–due-to-rising-adoption-by-telecom-companies-to-open-new-growth-avenues-in-multi-access-edge-computing-sector–million-insights-301225832.html
This article is subject to RADCOM’s disclaimers regarding Forward-looking statements and general information under the links below: